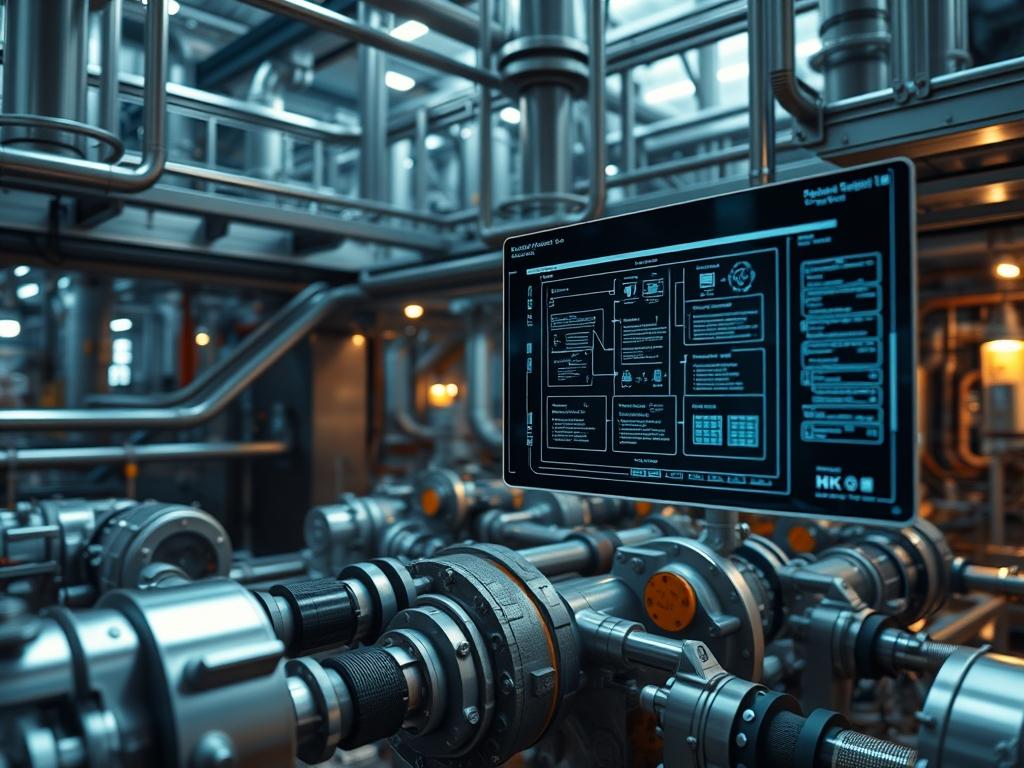
Geothermal Well Permit Standards function as the foundational protocol for sub-surface energy infrastructure; they dictate the lifecycle of high-enthalpy resource extraction. These standards act as the regulatory firmware that governs the interaction between mechanical assets and geological formations. In the modern technical stack, the permit process is no longer a localized paper-based exercise; it is an integrated data-driven workflow that links environmental compliance, geological safety, and mechanical integrity. The primary problem faced by project architects is the high latency between site exploration and legal authorization, which often results in significant capital overhead. By adhering to rigorous permitting standards, engineers ensure that the system architecture accounts for variables such as thermal-inertia and subsurface pressure differentials. This manual serves as a comprehensive guide to the technical specifications, configuration requirements, and troubleshooting procedures necessary to align a geothermal project with the highest industry and government benchmarks.
Technical Specifications
| Requirement | Default Port/Operating Range | Protocol/Standard | Impact Level (1-10) | Recommended Resources |
| :— | :— | :— | :— | :— |
| Casing Integrity | 3,000 to 8,500 PSI | API Spec 5CT | 10 | L80/P110 Carbon Steel |
| BOP Activation | 3,000 PSI Working Pressure | API Standard 16D | 9 | Dual-redundant PLC |
| Telemetry Feedback | 12Hz to 32Hz Sampling | IEEE 802.11ah | 7 | Quad-Core ARM / 8GB RAM |
| Thermal Threshold | 150C to 350C | ASTM E1066 | 8 | PEEK Insulated Sensors |
| Data Encapsulation | 256-bit AES Encryption | TLS 1.3 | 6 | Hardware Security Module |
| Flow Rate Logic | 50 to 250 Liters/Sec | ISO 10414-1 | 7 | Ultrasonic Flow Meters |
The Configuration Protocol
Environment Prerequisites:
Successful compliance with Geothermal Well Permit Standards requires a pre-configured environment that bridges physical hardware and digital control systems. All designers must verify the following dependencies:
1. Full adherence to API Spec 5CT for casing materials and API Standard 53 for blowout prevention.
2. Computational nodes running Linux Ubuntu 22.04 LTS or equivalent for SCADA integration.
3. Installation of GIS Desktop (ArcGIS or QGIS) with coordinate system EPSG:3857 for spatial mapping.
4. User permissions must be elevated to sudo for service management and Admin for resource registry portals.
5. Hardware interfaces must support Modbus TCP/IP for real-time sensor polling.
Section A: Implementation Logic:
The engineering design behind the permit standards relies on the principle of geological encapsulation. Since geothermal wells penetrate multiple aquifers and lithologies, the system must be designed as an idempotent series of barriers. Each casing string is treated as a discrete layer in a containerized environment; if one layer fails, the next layer must maintain the payload (the geothermal fluid) without secondary contamination. This design logic reduces signal-attenuation in pressure monitoring and ensures that thermal-inertia is calculated as a constant variable during high-throughput extraction phases. By modeling the well as a closed-loop packet-transfer system, we minimize the overhead of environmental impact and maximize the concurrency of energy production.
Step-By-Step Execution
1. Initialize Geodetic Validation
Execute the gdaltransform command to convert local survey coordinates into the standardized WGS84 format required by regulatory portals. Use the terminal command: gdaltransform -s_srs EPSG:4326 -t_srs EPSG:3857.
System Note: This action ensures that the physical drilling target aligns with the digital permit boundary; it prevents spatial collisions with existing mineral rights or protected aquifers at the kernel level of the GIS database.
2. Configure SCADA Gateway Permissions
Navigate to the configuration directory: cd /etc/geothermal/scada/ and modify the access control list using chmod 640 sensors.conf. This limits write access to the service account while allowing the monitoring daemon to read telemetry data.
System Note: Restricting permissions on the sensor configuration file prevents unauthorized modification of pressure thresholds; it ensures the integrity of the permit-mandated safety limits.
3. Deploy Telemetry Monitoring Service
Initialize the monitoring service by running systemctl start geothermal-telemetry.service. Verify the status using systemctl status geothermal-telemetry.service to ensure the PID is active and consuming less than 5% of CPU overhead.
System Note: This daemon polls the downhole sensors every 50ms; it translates raw voltage from thermal probes into formatted JSON payloads for the regulatory reporting dashboard.
4. Calibrate Pressure Transducers
Utilize a fluke-754 documenting process calibrator to source a known pressure to the honeywell-st-700 transmitter. Update the offset in the local controller using the command set-calibration –offset 0.042 –sensor-id P-101.
System Note: Physical calibration ensures that the digital twin of the well displays an accurate representation of the borehole pressure; this is a critical requirement for maintaining the blowout preventer standards.
5. Validate Blowout Preventer (BOP) Logic
Execute a logic-test on the Allen-Bradley PLC using the simulation command plc-test –unit BOP-01 –sequence emergency-close. Monitor the response time to ensure it falls under the 3-second limit.
System Note: This command triggers the physical solenoid valves in the BOP stack; it verifies the fail-safe logic required by the Geothermal Well Permit Standards without actually discharging the accumulator bottles.
Section B: Dependency Fault-Lines:
Systems often fail at the intersection of mechanical hardware and digital logic. A common bottleneck is the mismatch between the baud rate of downhole acoustic telemetry and the ingestion capacity of the surface gateway. If packet-loss exceeds 2%, the permitting software will flag the well as “Non-Compliant.” Furthermore, outdated versions of the OpenSSL library can lead to handshake failures between the wellhead sensor and the cloud-based regulatory database. Always ensure that the libssl-dev package is updated to the latest stable branch to prevent encryption-related downtime.
THE TROUBLESHOOTING MATRIX
Section C: Logs & Debugging:
When a permit-standard violation occurs, the monitoring system will trigger a specific fault code. Use the following paths and commands for rapid resolution:
– Primary Log Path: /var/log/geothermal/compliance.log
– Pressure Fault (Path E-102): Indicates a breach in the primary casing string. Check for signal-attenuation in the fluke-multimeter readings at the junction box.
– Thermal Overload (Error 505): Signifies temperatures exceeding the ASTM E1066 limit. Read the sensor dump using cat /dev/wellhead_temp | grep “status=critical”.
– Database Sync Failure: If the permit status does not update on the state portal, check the network throughput with iperf3 -c regulatory.gov.gateway.
If a visual cue on the HMI (Human-Machine Interface) shows a flickering red status on the “Annular Preventer,” inspect the physical hydraulic lines for leaks; then, reset the digital sensor state using systemctl restart bop-monitor.
OPTIMIZATION & HARDENING
– Performance Tuning (Thermal Efficiency):
Optimize the flow rate via the pid-control –tune command. Reducing the turbulence in the injection line decreases the energy overhead and maintains the thermal-inertia of the reservoir; this ensures long-term viability of the permit.
– Security Hardening (Permissions & Firewalls):
Implement a strict firewall policy using ufw allow from 192.168.1.50 to any port 502 proto tcp. This restricts Modbus traffic to the authorized PLC IP address only. All sensitive data within the permit_docs/ directory should be encrypted using gpg –encrypt –recipient admin@geotech.local.
– Scaling Logic:
When expanding from a single well to a multi-well pad, use a decentralized master-worker architecture. Deploy a Kubernetes cluster where each well is managed as a separate pod. This allows for high concurrency during data logging and ensures that a failure in one well’s telemetry does not cause a cascading failure across the entire project permit portfolio.
THE ADMIN DESK
How do I update the permit status manually?
Use the command permit-cli update –status “Active” –id [PERMIT_ID]. Ensure you have the signed PDF metadata file available in the /tmp/uploads directory; the system will verify the hash before committing the change to the ledger.
What is the solution for sensor signal-attenuation?
Check the physical connection for corrosion. If the hardware is intact, increase the gain on the signal amplifier using set-amp –gain +5db. Signal-attenuation often results from improper grounding of the RS-485 shielded cable.
How is thermal-inertia tracked for the annual report?
The system aggregates hourly temperature deltas in the /var/data/thermal_summary.csv file. Use a Python script with the pandas library to calculate the mean resistance to cooling; this report is vital for permit renewal.
Can I run the telemetry service on a Windows-based server?
While possible through WSL2, it is not recommended for production environments. The Geothermal Well Permit Standards require high-availability and low latency; a native Linux kernel handles the raw socket connections for Modbus and MQTT with significantly less overhead.
What happens if the BOP fails the weekly test?
The system will automatically transition to “Safe Mode” and lock the master valve. You must perform a manual reset on the logic-controller and log the mechanical intervention in the compliance.log file before resuming operations.