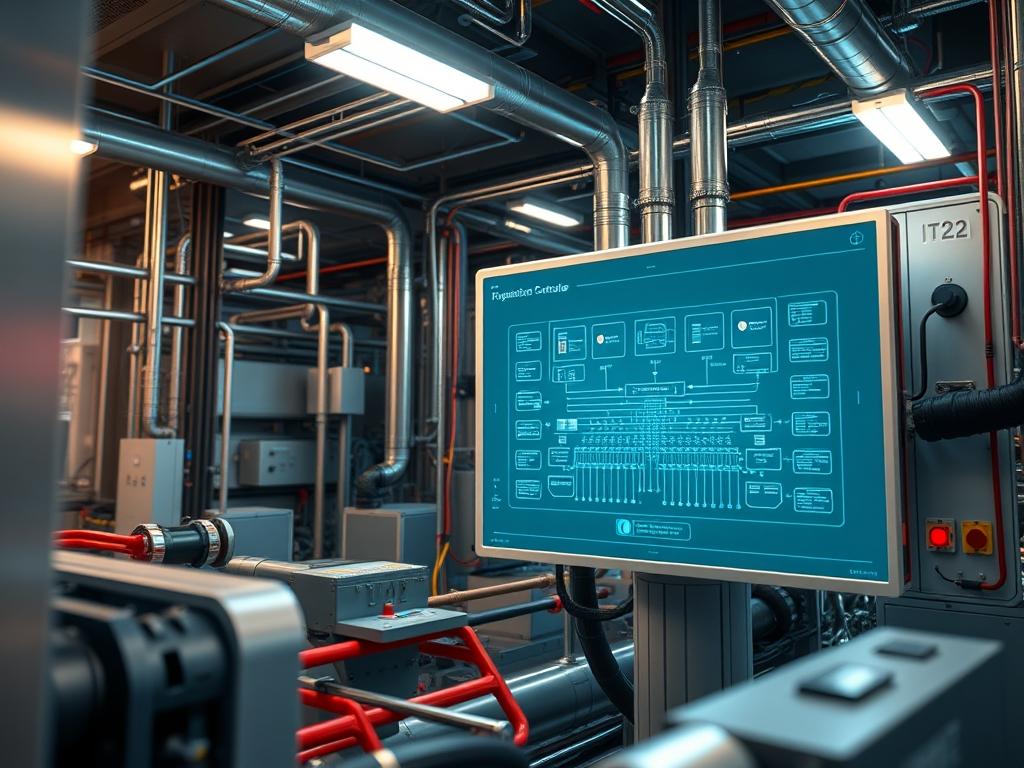
Heat Pump Logic Controller Firmware serves as the critical intelligence layer between physical thermodynamic processes and high level infrastructure management systems. In the context of industrial energy grids or large scale HVAC deployments; this firmware dictates the efficiency of heat transfer by modulating compressor speeds, expansion valve orifices, and fan velocities based on real time sensor inputs. The primary challenge in these environments involves balancing thermal inertia against rapid fluctuations in electrical grid frequency or localized demand. When firmware logic fails to account for mechanical latency; system oscillations occur, leading to premature component fatigue or total compressor seizure. Reliability maintenance requires a rigorous approach to firmware lifecycle management; ensuring that sensor telemetry is processed with minimal overhead and that safety overrides remain idempotent across all operational states. By centralizing control logic within a dedicated microcontroller unit (MCU), architects can isolate the high voltage power electronics from the communication stack; thereby reducing the risk of catastrophic failure during a network or logic fault.
Technical Specifications (H3)
| Requirement | Default Port/Operating Range | Protocol/Standard | Impact Level (1-10) | Recommended Resources |
| :— | :— | :— | :— | :— |
| I/O Bus Latency | < 10ms | Modbus RTU / RS-485 | 9 | ARM Cortex-M4 / 128KB RAM |
| Grid Integration | Port 502 (TCP) | IEEE 2030.5 / SunSpec | 7 | Linux-based Gateway / 1GB RAM |
| Sensor Accuracy | +/- 0.1 degree Celsius | ADC / I2C | 8 | Platinum RTD (PT1000) |
| Telemetry Uplink | Port 1883 (MQTT) | TLS 1.3 / JSON | 6 | High-Speed Ethernet / CAT6 |
| Flash Endurance | 100,000 Cycles | SPI / NOR Flash | 10 | Industrial Grade SLC NAND |
The Configuration Protocol (H3)
Environment Prerequisites:
Before initializing Heat Pump Logic Controller Firmware updates or configuration; the system must adhere to specific architectural standards. Ensure compliance with IEEE 1547 for grid interconnection and NEC Article 440 for cooling equipment safety. Hardware requirements include a dedicated JTAG/SWD interface for direct firmware flashing and a shielded USB-to-RS485 converter for bus monitoring. Software dependencies involve the GCC ARM Embedded Toolchain, OpenOCD for debugging, and a Python 3.x environment for running validation scripts. Users must possess sudo or administrative privileges on the maintenance terminal to access serial ports and system directories.
Section A: Implementation Logic:
The engineering design of Heat Pump Logic Controller Firmware centers on the Proportional-Integral-Derivative (PID) loop and its interaction with thermal-inertia. Unlike standard logic controllers; this firmware must account for the phase shift between the application of power to the compressor and the actual rise in refrigerant pressure. The logic uses a “feed-forward” mechanism to predict demand spikes, preventing the “hunting” effect where the system overcorrects and oscillates around the setpoint. Encapsulation of hardware abstraction layers (HAL) allows the core logic to remain independent of specific sensor brands; ensuring that signals from thermistor arrays or pressure transducers are normalized into a standardized floating point format before entering the PID calculation. This approach ensures high throughput for sensor data while maintaining a low memory footprint; vital for maintaining stability under high concurrency scenarios where multiple units are networked across a single building management system.
Step-By-Step Execution (H3)
1. Hard-Reset and Baseline Calibration
Initiate a physical hard reset of the MCU by pulling the NRST pin to ground for 500ms. Following the reboot; access the maintenance console via minicom -D /dev/ttyUSB0.
System Note: This action clears the volatile RAM and resets the program counter to the start of the bootloader; ensuring a clean state for firmware verification. It forces the system to re-read the calibration constants stored in the non-volatile EEPROM.
2. Integrity Verification of the Binary Image
Run the command sha256sum /firmware/hplc_v2.4.bin and compare the output against the manufacturer-signed manifest.
System Note: Verifying the payload hash prevents the execution of corrupt or malicious code. This step is critical for maintaining security hardening on the flash memory, as it ensures the kernel will not initialize if a bit-flip has occurred during transmission.
3. Flashing via OpenOCD
Execute the flashing command: openocd -f interface/jlink.cfg -f target/stm32f4.cfg -c “program hplc_v2.4.bin verify reset exit 0x08000000”.
System Note: This writes the binary directly to the internal flash at the specified memory address. The tool performs a bit-by-bit comparison post-write to ensure the integrity of the logic gates within the controller hardware.
4. Daemon Re-initialization
On the management gateway; restart the telemetry service using systemctl restart hplcd_gateway.service.
System Note: This command refreshes the local service that bridges the Modbus serial data to the cloud via MQTT. It clears any hung file descriptors and re-establishes the socket connection to the broker.
5. PID Parameter Validation
Use the command mosquitto_pub -t “hplc/config/pid” -m ‘{“p”: 1.2, “i”: 0.05, “d”: 0.1}’ to push new coefficients to the controller.
System Note: This updates the active control variables without requiring a reboot. The firmware consumes this payload and updates its internal registers; altering how the PWM (Pulse Width Modulation) signal drives the compressor inverter.
6. Thermal Load Testing
Monitor the real time output using tail -f /var/log/hplc/telemetry.log while increasing the setpoint by 5 degrees.
System Note: This allows the technician to observe the ramp-up behavior of the compressor. It checks the firmware for signal-attenuation or logic-loops during high-load transitions; ensuring the thermal-inertia management is functioning as designed.
Section B: Dependency Fault-Lines:
Reliability is often compromised by physical layer failures that present as firmware errors. Signal-attenuation on the RS-485 bus; caused by improper termination resistors or ground loops; can lead to intermittent packet-loss in the telemetry stream. If the firmware logic encounters too many cyclic redundancy check (CRC) errors; it may enter a “Fail-Safe” mode, cutting power to the compressor. Additionally; library conflicts within the gateway software (such as incompatible OpenSSL versions) can disrupt the encrypted uplink, leading to a “Buffer Overflow” as the controller continues to cache data that cannot be sent. Ensure all CAT6 cabling is routed away from high-voltage lines to prevent electromagnetic interference from corrupting the TTL logic levels.
THE TROUBLESHOOTING MATRIX (H3)
Section C: Logs & Debugging:
When a fault occurs; the first point of reference is the internal error log found at /var/log/hplc/kernel.log. Seek specific error strings such as “ERR_COMP_SHORT_CYCLE” which indicates the anti-restart timer has been triggered. If the logic controller is unresponsive; check the D1 LED on the PCB; a fast blink pattern (4Hz) typically indicates a watchdog timer reset, suggesting the code is caught in an infinite loop. For physical sensor errors; cross-reference the hex value in the log (e.g., 0xFA) with the hardware manual; 0xFA often denotes a disconnected thermistor. Use a fluke-multimeter to verify that the 5V DC rail is stable; ripples in the power supply can cause the ADC to produce erratic readings; which the firmware will interpret as rapid temperature swings, leading to erratic system behavior and reduced throughput.
OPTIMIZATION & HARDENING (H3)
– Performance Tuning: Use DMA (Direct Memory Access) for transferring sensor data from the ADC to the memory. This reduces CPU overhead and latency; allowing the controller to spend more cycles on complex PID calculations. Adjust the thread priority for the safety-monitoring task to ensure it is never preempted by telemetry tasks.
– Security Hardening: Implement iptables rules on the gateway to restrict access to the Modbus port (502) to only authorized IP addresses. Ensure the firmware uses a “Secure Boot” mechanism where the bootloader checks a cryptographic signature before jumping to the main application code. Set the read-only flag on configuration registers once calibration is complete.
– Scaling Logic: When managing a cluster of heat pumps; utilize an “Orchestrator” firmware that staggers the start times of compressors. This prevents “Inrush Current” spikes that can destabilize the local microgrid. Maintain a state-machine that synchronizes all units via a shared CAN-bus to ensure total system load does not exceed breaker capacity.
THE ADMIN DESK (H3)
How do I recover from a bricked firmware flash?
Connect a JTAG debugger and perform a full “Mass Erase” of the NOR Flash. Re-upload the factory-default binary image and recalibrate the EEPROM settings via the serial console using the factory_reset command.
What causes the “PID Overrun” error in the logs?
This happens when the calculation time for the control loop exceeds the defined sampling interval. Increase the MCU clock frequency or simplify the derivative calculations to ensure the logic completes before the next sensor interrupt.
Why is my telemetry showing 0 values intermittently?
Search for EMI-induced packet-loss on the RS-485 line. Ensure you are using twisted-pair cabling with a 120-ohm termination resistor at both ends of the segment to eliminate signal reflections and improve data integrity.
Can I update firmware while the compressor is running?
No. Firmware updates halt the PWM generation, which could leave the inverter in an undetermined state. Always put the unit into “Standby Mode” via systemctl stop hplcd before initiating a flash sequence to ensure mechanical safety.
How is the “Anti-Short Cycle” time determined?
It is hard-coded in the firmware as a constant (usually 300 seconds). This prevents the compressor from restarting too quickly after a shutdown; allowing pressures to equalize and protecting the motor from start-up torque damage under load.